This is a complete guide to the Caesar cipher and the tools you need to decode it. Learn about its famous history and where it is still in use today, or use the tool to solve it automatically.
The Caesar cipher, also known as a shift cipher, Caesar's code, or Caesar shift is one of the oldest and most famous ciphers in history. While being deceptively simple, it has been used historically for important secrets and is still popular among puzzlers.
Are you unsure that your cipher is a Caesar cipher? Use the Cipher Identifier to find the right tool.
Caesar Cipher Tool
Instructions
You can decode (decrypt) or encode (encrypt) your message with your key. If you don't have any key, you can try to auto solve (break) your cipher.
Settings
- Language: The language determines the letters and statistics used for decoding, encoding and auto solving.
- Max Results: This is the maximum number of results you will get from auto solving.
- Spacing Mode: This is about the spaces (word breaks) in the text. In most cases it should be set to Automatic. In case a specific letter (for instance X) is used as word separator, set it to Substitute.
Auto Solver options
Knowing the encryption key
Auto Solve results
| Score | Key | Text |
|---|
Still not seeing the correct result? Then try experimenting with the Auto Solve settings or use the Cipher Identifier Tool.
Cipher Description
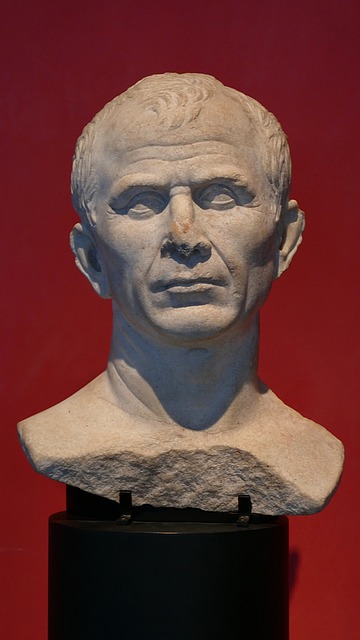
The Caesar cipher is named after the legendary Roman emperor Julius Caesar, who used it to protect his military communications. It is a simple substitution cipher, where each letter corresponds to another letter a certain number of positions forward or backward in the alphabet. For example, a shift right of 5 would encode the word Caesar as “hfjxfw”. Due to this simplicity, the Caesar cipher offers little security against those with even a passing knowledge of cryptography.
Example
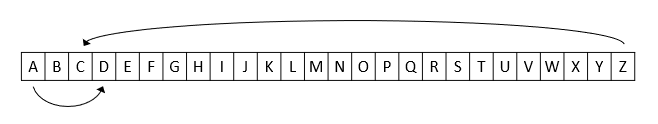
The easiest way to understand the Caesar cipher is to think of cycling the position of the letters. In a Caesar cipher with a shift of 3, A becomes D, B becomes E, C becomes F, etc. When reaching the end of the alphabet it cycles around, so X becomes A, Y becomes B and Z becomes C.
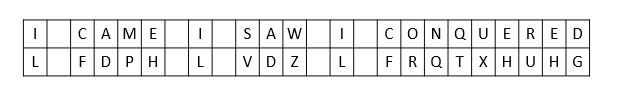
In this example the phrase “I came, I saw, I conquered” becomes “L FDPH, L VDZ, L FRQTXHUHG” once encoded with a shift of 3.
If you assign numbers to the letter so that A=0, B=1, C=2, etc, the cipher’s encryption and decryption can also be modeled mathematically with the formula:
En(c) = (x + n) mode 26
where x is the value of the original letter in the alphabet’s order, n is the value of the shift and 26 is the number of letters in the alphabet. In this formula n is positive during encryption and negative during decryption. A shift of 0 or 26 would obviously result in no encryption at all as the letters would simply shift to their original positions. Additionally, shifting twice equates to no extra security as shift values can be added together and be used as n.
Keyed Caesar Cipher
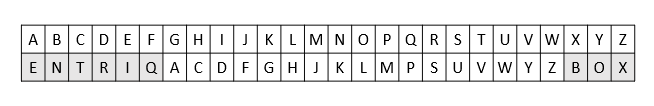
Due to its versatility, and ability to work with any alphabet, history has seen several variants of the Caesar cipher arise. In a slightly more secure variant, known as a keyed Caesar cipher, one writes a passphrase out, ignoring duplicate letters, then writes the remaining letters of the alphabet. Finally, all letters are shifted like in an ordinary Caesar cipher. This is more secure due to the more complex pattern of the letters.
A Keyed Caesar Cipher tool is available here.
Below is an example using the key BOXENTRIQ and a right shift of 3.
Breaking the Cipher
The Caesar cipher, while reasonably effective in its Roman heyday, is now one of the easiest cryptographic codes to break. Breaking a Caesar cipher usually follows one of three scenarios depending on the amount of knowledge the attacking cryptanalyst has:
- The cryptanalyst knows that the cipher is a Caesar cipher.
- The cryptanalyst knows that the cipher is substitution cipher, but not a Caesar cipher.
- The cryptanalyst is totally unaware of the kind of cipher they are faced with.
In all of the proposed scenarios, assuming that the cipher relies on a simple numerical shift, the code can very easily be cracked using a brute force attack (trying all possible shifts and determining which one works). In the case of a keyed Caesar cipher, matters become considerably more difficult, though still relatively easy to break. In this instance there are two primary methods of breaking the code:
- One method is to create a list of words that could be the possible key phrase and attempt a brute force attack.
- Another method is to employ frequency analysis. This is the standard method for breaking any substitution cipher. The most common letters in the English alphabet are E and T, so they are likely represented by the most common letters in the cipher.
History
The Caesar cipher is one of the oldest forms of cryptography in recorded history, with instances stretching back long before it was first named. Nonetheless, the cipher finds itself named for, and consistently associated with, the famous Roman Emperor and General Julius Caesar. It was Caesar who reportedly used the cipher with a shift of three to encode military messages to his commanders while on a campaign. After his assassination, Caesar's nephew Augustus carried on his uncle’s usage of the cipher to protect his correspondence but changed his messages encryption to a right shift of one. Despite the presence of more complex codes, the cipher was likely favored by the emperors due to its simplicity. The cipher was likely effective due to the illiteracy of many of those who would intercept them and a common misconception that the messages were written in a mysterious foreign language. Enforcing this assumption of security is the lack of evidence that any methods for solving substitution ciphers existed at the time, with the first instances of frequency analysis appearing in the middle east centuries after Caesar's death.
Despite its growing ineffectiveness in the modern era, the cipher would nonetheless remain in use by various groups for less vital communications such as by Jewish groups to encrypt the name of god on the mezuzah and later by people wishing to exchange messages in plain view by posting encoded passages in newspapers. Nevertheless, the last major use of the cipher for warfare was by imperial Russian forces in the first world war due to the common soldiers struggling to understand more complex encryption methods. A choice that was found to be a failure as contemporary German and Austrian code-breakers were easily able to decipher any messages sent in the code.
Regardless of being phased out well over a century ago, the Caesar cipher has not fallen out of use entirely. In 2006 a Sicilian mob boss named Bernardo Provenzano was captured by police due to his usage of an altered version of the Caesar cipher where letters were replaced by numbers after their shift. Likewise in 2011, a British counter-terrorist operation foiled a planned airline bombing due to the usage of an easily breakable Caesar cipher by the perpetrators in their internet communications.
Usage
Despite its lack of security in helping to send confidential communications by itself the Caesar cipher still has several applications today in a variety of fields. This is due to its versatility in acting as both a simple code for education and fun and as a building block for more complex encryptions:
- The ROT13 system is a special case of the Caesar cipher that operates on a shift of 13. Beginning in the 1980s with the net.joke newsgroup and continuing to the modern day, ROT13 is commonly used on online forums to hide, punchlines, plot points, and puzzle solutions in discussions to prevent spoilers.
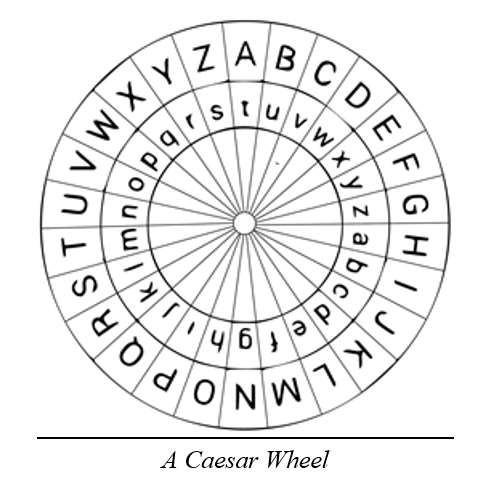
- Caesar ciphers are commonly used in children's decoder rings to create simple codes and puzzles to teach cryptanalysis. Notably, decoder rings themselves are a modern version of the Caesar wheel, an early decryption tool used to break the Caesar cipher.
- The Caesar cipher, while laughably easy to break for even the most novice modern cryptanalyst, forms a key part of the much more difficult to break Vigenère cipher. A cipher which took nearly 3 centuries to break and operates on interweaving different alphabets with several Caesar ciphers.
- The Caesar cipher forms the basis of the unbreakable one-time pad cipher.
Trivia
- While the Caesar cipher is named for Julius Caesar due to his extensive application of the code, there are instances of other substitution ciphers predating his life by decades.
- Lovers would use Caesar ciphers to exchange messages in plain sight through placing encoded ads in newspapers such as The Times during the 19th century
- Ironically, while Caesar ciphers are not very secure by themselves, they are a common component of much more complex encryption techniques including the Vigenère cipher and the unbreakable one-time pad cipher.
- While the Jewish mezuzah commonly employs a Caesar cipher to encrypt the names of god, the cipher letters themselves are considered a divine name in their own right, with the power to hold the forces of evil in check.
- The army of the Confederate States of America in the American civil war used a form of the keyed Caesar cipher to encrypt military messages. Though it was later broken using advanced frequency cryptanalysis due to its short key phrase of “Complete Victory”.
- Julius Caesar was known for his extensive usage and development of codes. Indeed, he was so prolific in the field that the grammarian Probus wrote a treatise on them that is now lost.
- The Caesar cipher lost most of its effectiveness even with advanced protocols with the discovery of frequency analysis in the 9th century.
Though advanced for its time the Caesar cipher is now one of the easiest codes to break. Using the information found here those stuck on any variant of the cipher will find that solving it is often as simple as a shift of one or two or three or perhaps 13! After all, no matter the complexity a true puzzler will find a solution.
Sample Caesar Cipher
Code-breaking is not only fun, but also a very good exercise for your brain and cognitive skills. Why don’t you try breaking this example cipher:
vkbxw whkhmar tkx rhn ghm t zkxtm pbstkw anla fr wxtk ax ltbw whgm lixtd lh ehnw hk rhn pbee ux hoxkaxtkw tgw b lahnew ux knbgxw
See also: Code-Breaking tools | Adfgvx cipher | Adfgx cipher | Affine cipher | Atbash cipher | Baconian cipher | Beaufort cipher | Bifid cipher | Columnar transposition | Cryptogram | Double transposition | Enigma machine | Four-square cipher | Gronsfeld cipher | Keyed caesar cipher | One-time pad | Pigpen cipher | Playfair cipher | Rail fence cipher | Rot13 | Route transposition | Substitution cipher | Trifid cipher | Variant beaufort cipher | Vigenere cipher